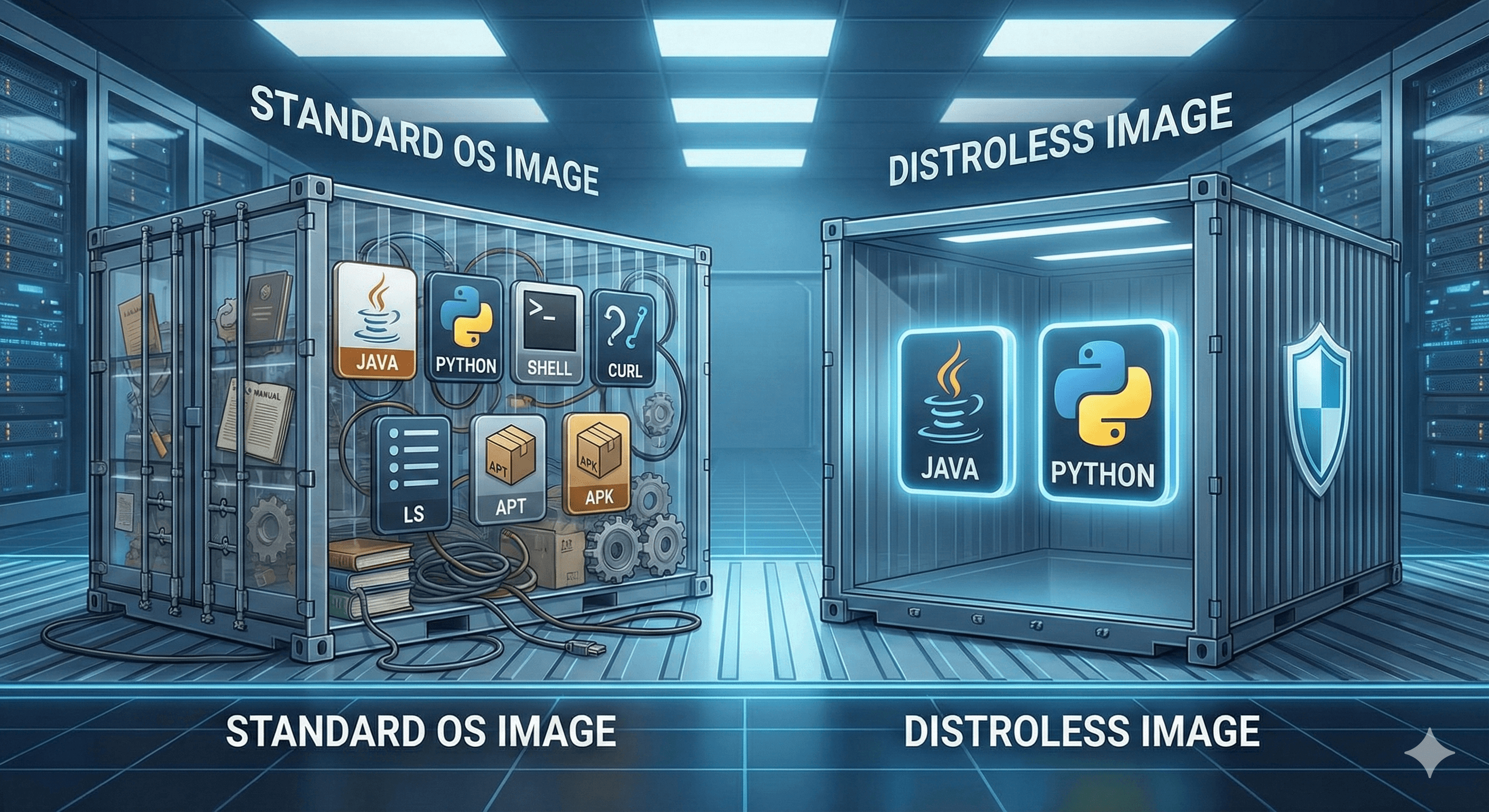
Shrink Your Attack Surface with Distroless Images
#🚨 The Problem: Production Bloat
We love alpine for its size and ubuntu for its familiarity. But in production, why does your Node.js application need curl, bash, or apt-get?
Every extra binary in your container is a potential tool for an attacker if they compromise your application. If they break in, don't hand them a toolbox.
#🛡️ The Solution: Distroless Images
"Distroless" images are ultra-minimal. They contain only your application and its direct runtime dependencies (like libc or a JVM).
What makes them secure?
If you found this helpful, please like and share to support the content!
Comments (0)
Leave a comment
About MjShetty
Always curious to understand the concept, learning by breaking and fixing, and passionate about sharing knowledge with the community.Get in touch with me→