How to Debug Google Distroless Images: A Zero-to-Hero Guide
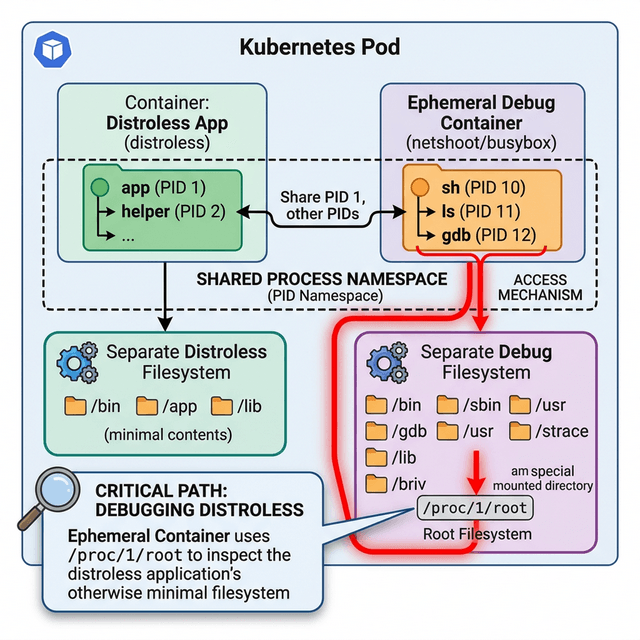
You switched to Distroless for the security wins and smaller footprint. But now your pod is crashing, and kubectl exec throws an error because there is no shell. Here is the production-grade way to get inside.
#🔒 The Distroless Dilemma
Distroless images (gcr.io/distroless/*) strip out everything that is not your application runtime: no /bin/sh, no apt, no apk. That is the point. A smaller attack surface means fewer CVEs.
The trade-off hits you the moment something breaks in production:
OCI runtime exec failed: exec failed: container_linux.go:345:
starting container process caused: exec: "sh": executable file not found in $PATHYou cannot kubectl exec into the container because there is nothing to exec into. Here are three methods to solve this, ordered by how often you will use them.
#🛠️ Method 1: The Production Way (kubectl debug)
If you found this helpful, please like and share to support the content!
Comments (0)
Leave a comment
About MjShetty
Always curious to understand the concept, learning by breaking and fixing, and passionate about sharing knowledge with the community.Get in touch with me→