Docker Hardened Images (DHI) - Moving from DIY Security to Hardened by Default
Even if you use a minimal image, how do you prove it hasn't been tampered with? How do you know exactly what’s inside it? In regulated industries (Finance, Gov, Healthcare), "trust me" isn't an architecture. You need proof of origin and a way to handle the constant noise of "unexploitable" vulnerabilities.
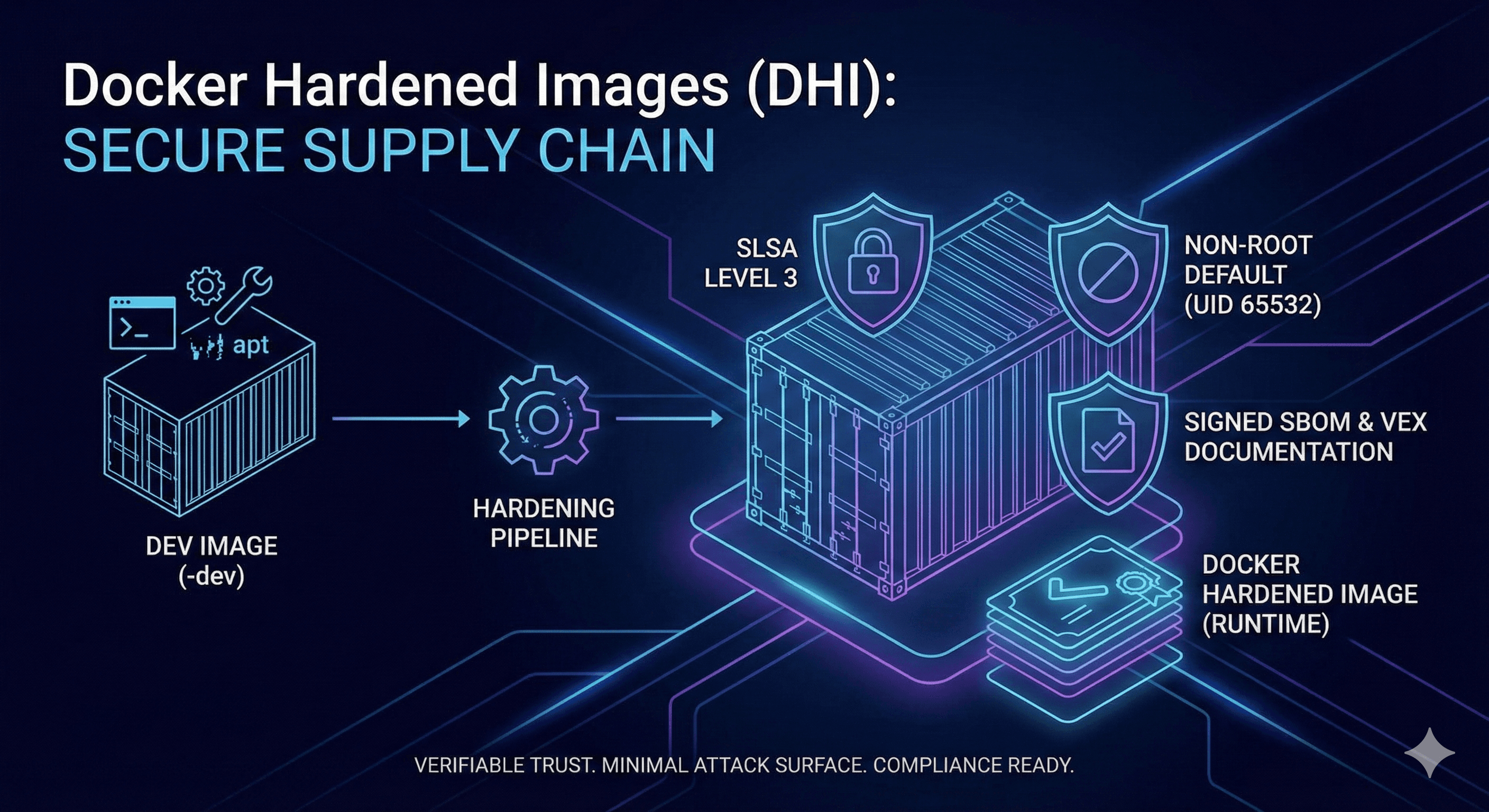
#🏗️ The Hardened Blueprint: Core Features
Docker Hardened Images are built on four "Secure-by-Default" pillars:
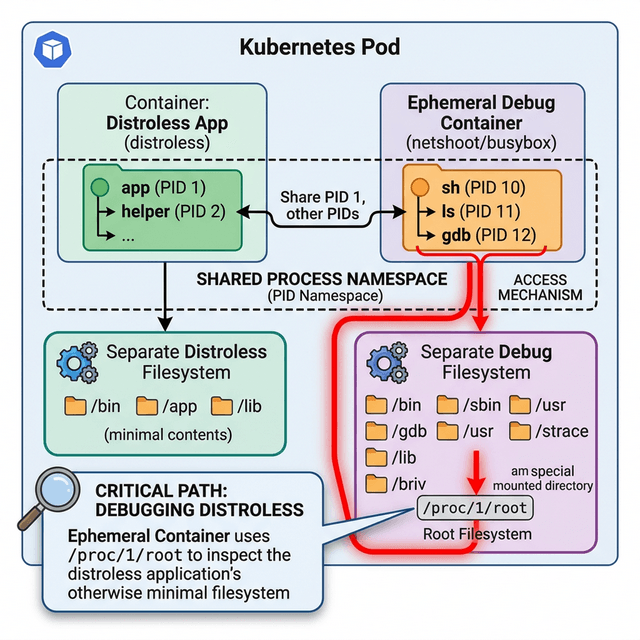
- Zero-Overhead Design: Like Distroless, they remove shells, package managers, and tools. They are Non-Root by default (running as UID 65532), ensuring that even if an app is compromised, the attacker has no privileges.
- SLSA Level 3 Provenance: This is a cryptographic "birth certificate." It proves the image was built in a secure, tamper-proof environment and hasn't been modified since.
- Signed SBOMs: A built-in "Software Bill of Materials" that lists every single library and dependency. You don't have to guess what's inside; you have a signed manifest.
- VEX (Vulnerability Exploitability eXchange): The "Noise Filter." VEX documents tell your scanner: "Yes, this library is present, but it's used in a way that isn't exploitable." This stops your team from wasting hours chasing false positives.
#🛠️ The Developer Workflow: Dev vs. Runtime
Hardened images don't have to be hard to use. Docker provides a :
If you found this helpful, please like and share to support the content!
Comments (0)
Leave a comment
About MjShetty
Always curious to understand the concept, learning by breaking and fixing, and passionate about sharing knowledge with the community.Get in touch with me→